
- Kerkhoff Technologies
- Cybersecurity
- LogoFAIL a new firmware attack
Contact Us To Schedule Your Discovery Call
Follow us on Social Media

Ars Technica reported a new firmware attack called LogoFAIL that targets Windows or Linux computers. This attack is very effective because it changes the logo that shows up when the system boots after a successful POST (that’s why it’s called “LogoFAIL”), which is so early that it can avoid security measures that stop bootkit attacks.
Any motherboards that use UEFI from Independent BIOS Vendors (IBVs) are affected by this issue. IBVs like AMI, Insyde, and Phoenix have to release UEFI patches to motherboard companies. LogoFAIL can run on any platform that uses Intel, AMD, or ARM and any Windows operating system or Linux kernel because of how the boot logo that can be changed is run when the system turns on. It affects both DIY and prebuilt systems with some functions left open by default.
Researchers at Binarly found the exploit and published their results. The exploit happens when the ‘Driver Execution Environment’ (DXE) phase is going on after a successful POST. The DXE loads boot and runtime services, starts the CPU, chipset, and other components in the right order for the boot process to go on. LogoFAIL puts the exploit instead of the UEFI boot-up logo, which then runs during the DXE phase.
The researchers showed how it works and what it does on a Lenovo ThinkCentre M70s with an Intel 11th gen CPU, Intel Secure Boot and Boot Guard on, and the newest UEFI update from June.
How it works
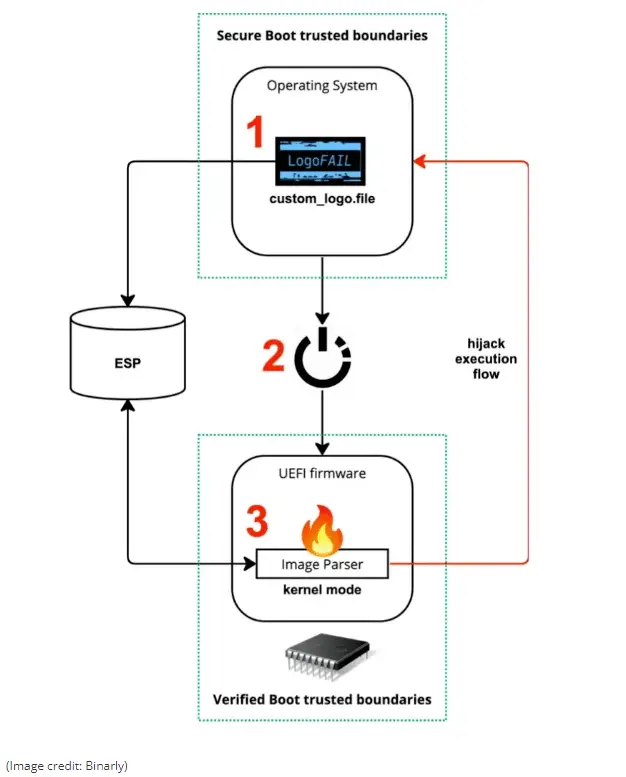
Alex Matrodov, the founder and CEO of Binarly, said that this exploit uses a new vulnerability in the image-parsing libraries that the UEFI uses during the boot process. LogoFAIL uses that vulnerability to get past all security solutions that the CPU, operating system, and any third-party security software have. The exploit is not on the storage drive, so the infection can’t be removed, even if you reformat the OS. This exploit at the UEFI level can then put a bootkit without any security layer stopping it — which makes it very dangerous (and a very good way to deliver it).
Macs and some prebuilt PCs are not affected.
Some OEMs, like Dell, don’t let their logos be changed in the UEFI — and their image files are safe with Image Boot Guard; these systems are not affected by this exploit. Macs, which have hardware and software made by Apple, have logo images that are fixed in the UEFI and are also safe. This is true for Macs that use Intel CPUs (fixed logo images), so those Macs are also not affected.
If your system integrator doesn’t let you change boot images in its BIOS, you should be okay. But for everyone else, this exploit has to be fixed by both motherboard manufacturers and OEMs, because the research shows both are at risk. The only way to keep the image parsing in your system’s UEFI safe is by getting a new UEFI security patch, which you have to get from your motherboard manufacturer or OEM (who will get it from the IBV).
AMI, Insyde, and Lenovo, and others, have given warnings, but there’s no full list of companies that are affected.
To find out if your system is at risk, you have to check with your OEM/motherboard manufacturer.
The business owner's guide to IT management
and support services
Questions you MUST ask before you hire an IT consultant and
enter into an IT service agreement.


